Now it seems that the massive amounts of traffic generated by this type of attack have even set off alarms at CERT (Cyber Emergency Response Team) in Poland. You see in order to affect the swarm in any measurable way they have to either send massive amounts of disconnect, end or file or false IP addresses to the other clients in the swarm. This means they would have to forge these packets and then flood them into the group to make sure they reach all of the members in the swarm.
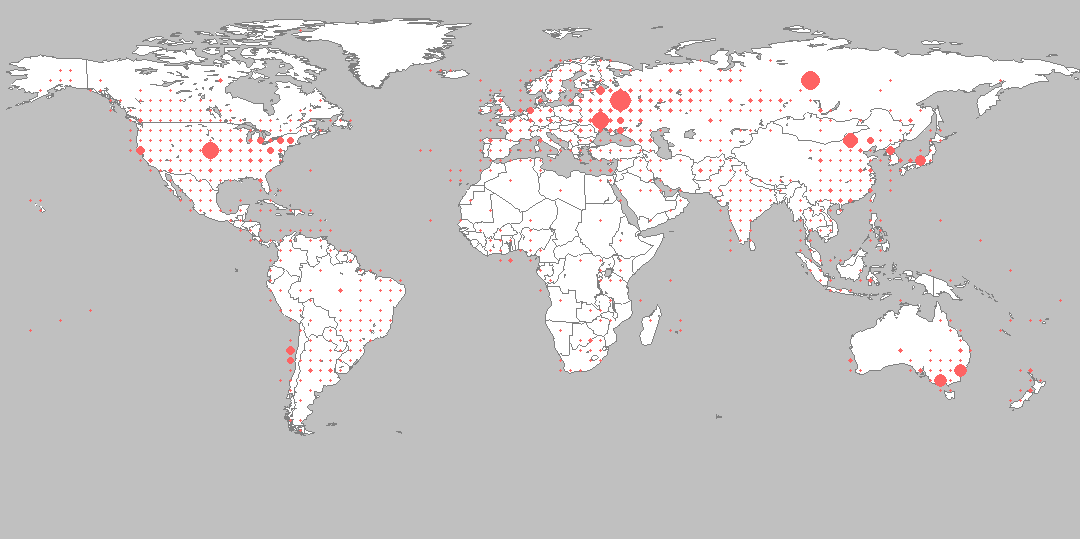
As of right now the targets are all torrent swarms that are for Russian movies (which is why Pirate Pay comes to mind). However, these massive injections of bad packets are not just coming from (the) Rodina (Mother Russia). CERT Poland has also identified origins in China, Canada, Australia, and the good old US.
Now what makes all of this even more interesting is that at least one of these companies has received money from a major copyright holder (Microsoft Russia). The Pirate Pay was given startup money to begin their venture into stopping piracy with their packing flooding technique. We wonder how many other companies are doing the same thing (providing money for the forming, maintenance, or continued operation) with other anti-piracy companies. Considering the fact that many people (including both legal and Cybersecurity experts) are questioning the legality of this type of action it would mean that Microsoft and anyone else that funded or paid for these services would be guilty of committing a crime as well. Now wouldn’t that be interesting to see the big copyright holders get slapped with Cease and Desist orders…
Of course they can always lobby for a law that says it is ok as long as it is for “anti-piracy” purposes and then forget to define what that means. In the meantime, it means that torrent users will find another way to do the same thing and the race will be on again.
Discuss this in our Forum

 About a week ago we first learned of a Russian company called
About a week ago we first learned of a Russian company called