From The Blog
-
ConnectWise Slash and Grab Flaw Once Again Shows the Value of Input Validation We talk to Huntress About its Impact
Written by Sean KalinichAlthough the news of the infamous ConnectWise flaw which allowed for the creation of admin accounts is a bit cold, it still is one that…Written on Tuesday, 19 March 2024 12:44 in Security Talk Read 684 times Read more...
-
Social Manipulation as a Service – When the Bots on Twitter get their Check marks
Written by Sean KalinichWhen I started DecryptedTech it was to counter all the crap marketing I saw from component makers. I wanted to prove people with a clean…Written on Monday, 04 March 2024 16:17 in Editorials Read 1567 times Read more...
-
To Release or not to Release a PoC or OST That is the Question
Written by Sean KalinichThere is (and always has been) a debate about the ethics and impact of the release of Proof-of-Concept Exploit for an identified vulnerability and Open-Source…Written on Monday, 26 February 2024 13:05 in Security Talk Read 1102 times Read more...
-
There was an Important Lesson Learned in the LockBit Takedown and it was Not About Threat Groups
Written by Sean KalinichIn what could be called a fantastic move, global law enforcement agencies attacked and took down LockBit’s infrastructure. The day of the event was filled…Written on Thursday, 22 February 2024 12:20 in Security Talk Read 1071 times Read more...
-
NetSPI’s Offensive Security Offering Leverages Subject Matter Experts to Enhance Pen Testing
Written by Sean KalinichBlack Hat 2023 Las Vegas. The term offensive security has always been an interesting one for me. On the surface is brings to mind reaching…Written on Tuesday, 12 September 2023 17:05 in Security Talk Read 2121 times Read more...
-
Black Kite Looks to Offer a Better View of Risk in a Rapidly Changing Threat Landscape
Written by Sean KalinichBlack Hat 2023 – Las Vegas. Risk is an interesting subject and has many different meanings to many different people. For the most part Risk…Written on Tuesday, 12 September 2023 14:56 in Security Talk Read 1839 times Read more...
-
Microsoft Finally Reveals how they Believe a Consumer Signing Key was Stollen
Written by Sean KalinichIn May of 2023 a few sensitive accounts reported to Microsoft that their environments appeared to be compromised. Due to the nature of these accounts,…Written on Thursday, 07 September 2023 14:40 in Security Talk Read 2111 times Read more...
-
Mandiant Releases a Detailed Look at the Campaign Targeting Barracuda Email Security Gateways, I Take a Look at What this all Might Mean
Written by Sean KalinichThe recent attack that leveraged a 0-Day vulnerability to compromise a number of Barracuda Email Security Gateway appliances (physical and virtual, but not cloud) was…Written on Wednesday, 30 August 2023 16:09 in Security Talk Read 2089 times Read more...
-
Threat Groups Return to Targeting Developers in Recent Software Supply Chain Attacks
Written by Sean KalinichThere is a topic of conversation that really needs to be talked about in the open. It is the danger of developer systems (personal and…Written on Wednesday, 30 August 2023 13:29 in Security Talk Read 1877 times Read more...
Recent Comments
- Sean, this is a fantastic review of a beautiful game. I do agree with you… Written by Jacob 2023-05-19 14:17:50 Jedi Survivor – The Quick, Dirty, and Limited Spoilers Review
- Great post. Very interesting read but is the reality we are currently facing. Written by JP 2023-05-03 02:33:53 The Dangers of AI; I Think I Have Seen this Movie Before
- I was wondering if you have tested the microphone audio frequency for the Asus HS-1000W? Written by Maciej 2020-12-18 14:09:33 Asus HS-1000W wireless headset impresses us in the lab
- Thanks for review. I appreciate hearing from a real pro as opposed to the blogger… Written by Keith 2019-06-18 04:22:36 The Red Hydrogen One, Possibly One of the Most “misunderstood” Phones Out
- Have yet to see the real impact but in the consumer segment, ryzen series are… Written by sushant 2018-12-23 10:12:12 AMD’s 11-year journey to relevance gets an epic finish.
Most Read
- Microsoft Fail - Start Button Back in Windows 8.1 But No Start Menu Written on Thursday, 30 May 2013 15:33 in News Be the first to comment! Read 116516 times Read more...
- We take a look at the NETGEAR ProSafe WNDAP360 Dual-Band Wireless Access Point Written on Saturday, 07 April 2012 00:17 in Pro Storage and Networking Be the first to comment! Read 87451 times Read more...
- Synology DS1512+ Five-Bay NAS Performance Review Written on Tuesday, 12 June 2012 20:31 in Pro Storage and Networking Be the first to comment! Read 82004 times Read more...
- Gigabyte G1.Sniper M3 Design And Feature Review Written on Sunday, 19 August 2012 22:35 in Enthusiast Motherboards Be the first to comment! Read 80317 times Read more...
- The Asus P8Z77-M Pro Brings Exceptional Performance and Value to the Lab Written on Monday, 23 April 2012 13:02 in Consumer Motherboards Be the first to comment! Read 70964 times Read more...
Displaying items by tag: Flash
Flash is certainly on its way out, but will that really fix much?
Last week Google announced that they will no longer be accepting ads that feature Flash. This new should really come as no surprise as Flash (and its spirit brother Java) have taken a beating on the security front for years. Abobe and Oracle have been unable to keep the bad guys from running rampant with their code. Of course the change will not take place overnight so everyone has the chance to swap out that old and insecure Flash for the new and (insecure) HTML5.
After multiple 0-days, many call for Flash to go away
After three spate 0-day vulnerabilities are found in your product you can pretty much expect the market to call for you go away. This is the situation that Adobe is in right now. After fighting to their little slice of dominance in the computing industry Adobe’s Flash is arguably one of the most commonly used APIs to rendering rich content. This has made them a rather large target for a number of years… well this and the fact that the Flash development team has made some rather poor choices when it comes to their application.
New Flaw found in Flash Player, yes another one.
Although it will not come as a surprise, there seems to be yet another bug in Adobe’s flash player that allows for an attacker to potentially take control of a system by forcing a crash of the application. According to TrendMicro, CVE 2015-5123 is a critical bug in the latest version of Flash player for Linux, Windows, and OSX operating systems. Adobe has already released a customer advisory stating they are already aware of this flaw being exploited in the wild.
Patriot talks about memory, portable power and a few other things at CES 2015
CES 2015 Las Vegas, NV Patriot Suite Bellagio
Stopping by the Patriot suite at the Bellagio we found Patriot talking about some pretty cool new items in addition to their normal memory products. We kicked off our meeting with a walk through of their flash memory products.
20 X NAND-Flash Endurance! NVMdurance debuts at FMS
The Flash Memory Summit wound down on Thursday after a four day run at the Santa Clara Convention Center in San Jose. The show floor was fairly crowded with over 5,000 attendees and a sold out exhibition space.
Corsair has started selling Force LX SSDs
Corsair has introduced a new series of solid state drives called Force LX , which currently consists of two models. Corsair Force LX family is made from 128GB (CSSD-F128GBLX) and 256GB (CSSD-F256GBLX) SSDs, both coming in the same classic 2.5 inch package and 7 millimeters thick. Mentioned models have data read speed of 560 MB/s, while the write speed depends as ever about the capacity of the SSD.
Toshiba drops a few new SSDs on the market
New Toshiba SSDs belong to HG6 Series, have a SATA 6.0 Gbps interface and should appear on the market in March this year with yet unknown prices. During manufacture Toshiba decided to incorporate NAND chips that are created in the 19nm technology of 2nd generation. SSDs will be available in 2.5-inch mSATA and M.2 (single and double) packaging, and in capacities from 60 GB to 512 GB.
Bigger, Faster, Cheaper Flash in Demand But Cold?
 |
“By the time you get this message, I'll be in the dead zone.” – Capa, “Sunshine,” DNA Films, 2007
You have to wonder if this year’s Flash Memory Summit (FMS) didn’t have Al Shugart, a hard drive pioneer, spinning in his grave.
There are a whole lot of silicon engineers hell-bent on moving his technology to a dusty corner of the Computer Museum.
Shugart was a key developer of IBM’s RAMAC (Random Access Method of Accounting and Control) disk system that stored a whopping 5MB of data. Today, no kid would look twice at a smartphone or tablet if it didn’t have at least 32GB (1GB = 1,024MB).
Samsung shows off first SSDs with 3D memory chip
 |
After Samsung introduced the first "vertical" 3D memory chip earlier this month it did not take long for the first concrete product using this technology to appear. They launched SSDs of 960 and 480 GB, which are designed for enterprise servers and data centers.
New Storage Technologies Could Make Our Mobiles Faster; Meet RRAM and 3DNAND
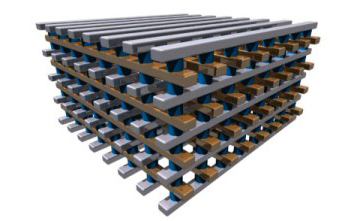 |
In almost every consumer electronics device there is a bottleneck for performance. It is not always the same item for each family (or even different devices within the same family), but it is always there. In the mobile this bottle neck was the CPU followed by memory. Now mobile devices are running into the same problems that desktops hit about 5 years ago. The performance provided by current storage technologies is being out stripped by CPU (SoC), memory, and even usage patterns of mobile device users. They are demanding more space, more speed and all with better power consumption.




