Displaying items by tag: FBI
US Federal Civilian Executive Branch Agency’s Email Compromised by new Chinese APT Group
It seems that an unnamed FCEB agency had their Outlook Web Access (Exchange Online) environment compromised by a new threat group that is current being attributed to China. The attack and the group were disclosed by CISA and the FBI. With the detection of the FCEB email compromise, Microsoft also identified a much larger espionage campaign involving the newly identified group which includes some 20+ organizations. The timing of the attack is concerning due to it coinciding with a recent NATO meeting.
New APT Group targeting iOS Users with Zero-Click Malware, US gets the Blame
There is a new bit of malware targeting iOS users via iMessage from what appears to be a new APT (Advanced Persistent Threat) group. The campaign appears to have been in play since some time in 2019. The malware, according to researchers, leverages iMessage to send the targeted user an attachment that then runs with Root Privileges on the device. The result is a complete takeover of the device in question.
Law Enforcement Celebrates Another Hacker Forum Takedown as the Seizure of RaidForums is Announced.
2022 has been a busy year for the information security industry on both sides of the playing field. We have seen an increase in target attacks on businesses, a larger number of Zero-Day vulnerabilities disclosed that were being actively exploited in the wild, several major companies had data stollen and leaked, and we cannot forget the threat actor war going on over the Russian Invasion of Ukraine. With all these items, law enforcement agencies have also been very busy with the seizure and shut down of two major “hacker” marketplaces, Hydra and RaidForums.
FBI Sent out an Advisory Alleging a Targeted Campaign Against State Election Officials
The FBI, on March 29th, released a Private Industry Notification with vague details on a potential Phishing campaign targeting election officials in at least nine US states. The information in the advisory gives very broad information without really saying much. There is no information in the notification on which states were targeted and the phishing campaign sounds a lot like ones that are sent out to millions of people every day.
Joint Advisory from the NSA, FBI and CISA Warns of Long-Term Attack by State Actors with Little Detail.
Life would not be the same without new popping up that one state level threat actor or another was attacking and compromising US defense contractors or other businesses linked to US national security and defense. The counties of origin for these actors become a blur over time, although you do see some highlighted depending on current political trends. The two most often bandied about are Russia and China with North Korea getting an honorable mention.
The FBI hides collection of Iris information by local law enforcement since 2013
In the last week the world saw what appeared to be another attempt to violate privacy by government law enforcement. In this case the FBI opened a “pilot” program to capture iris imprints for a searchable database. To date they have captured more than 400,000 of these imprints. The major concern here is that there was (and remains) no public debate, or oversight on the program. The program stands on its own outside the many restrictions that protect privacy and also other rights that people have. Well at least that is how things look on the surface. We took a little bit of a deeper look and tried to peel away some of the FUD and hype over the collection.
Privacy: it doesn’t mean what you think it means
The term privacy has come to mean a great many things in the last few years. To some the idea of privacy is being able to do or say certain things without the fear of anyone finding out. Most people like to know that what they do on their own time is their business. Where things get a little muddy is when people liken the desire for privacy with a desire to hide wrongdoing. This belief couldn’t be farther from the truth . It is not just that it is wrong, but it is also dangerous. To imply that anyone that wants to have privacy is somehow hiding something illegal sets a dangerous precedent. Keeping this mentality alive will allow for a further erosion of peoples’ rights and grants very worrying powers to agencies that are there to protect, not to oppress.
Sony hack was probably not from Korea… Go figure
So the big Sony Hack that everyone was talking about and that the US government blamed on Korea might not have been state sponsored after all. Despite the FBI’s initial (and way too fast) conclusion that the source of the attacks were from North Korea there was ample evidence that this was not the case from the start. Anyone familiar with the way an attack happens knows that the majority are going to be pushed through multiple proxies and will have some sort of obfuscation to hide who is doing what including using code that might have been used before.
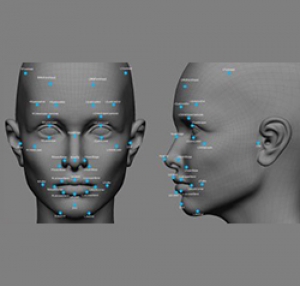
FBI creating database with 52 million facial photos
The organization Electronic Frontier Foundation (EFF) announced their concern that the U.S. Federal Bureau of Investigation (FBI) is planning in the near future to have a visual database with photographs of people's faces.
Malware Used to Identify People on the Tor Network...
 |
The news is all abuzz with the compromise of the Tor (Originally The Onion Router) Network. This network has been used by a wide variety of people who are looking for a degree of anonymity. It relies on the use of different entry and exit point to prevent someone from identifying your exact IP Address or MAC address. In-between these point there are different hops that further confuse the trail. In basic terms your system is masked by the exit point which is selected randomly by the system. Now in addition the anonymity services for individual users there are also servers that host websites and even anonymous email services. Some have called this the “dark net” or “deep web” although that is not actually the case (the dark net is something else entirely). Many of these sites are legitimate sites that need to protect their readers from less than understanding authorities, but there are a larger number that are not above board at all including many sites that host child pornography.