The details of the attack have not been released, but we can tell you that from a trace route run to the CIA’s site there is no response after a hop on Alter.net’s end of the trip. This is interesting as we are still getting resolution of the site IP, but the site is not talking. This is most likely a DDoS (Distributed Denial or Service) attack on the site and could go on for a long time depending on how long it takes the CIA and NSA to kill off the bots that are flooding the servers with noise.
This attack follows on the heels of attack on the Department of Justice, the US Copy Right Office and the FBI. Those attacks were in response to the take down of MegaUpload. As far as the attack on the CIA we are not at all certain for the reasons here. Honestly it could be random, but it could also be a reminder of how easy it is to do this sort of thing and what kind of power Anonymous can throw around.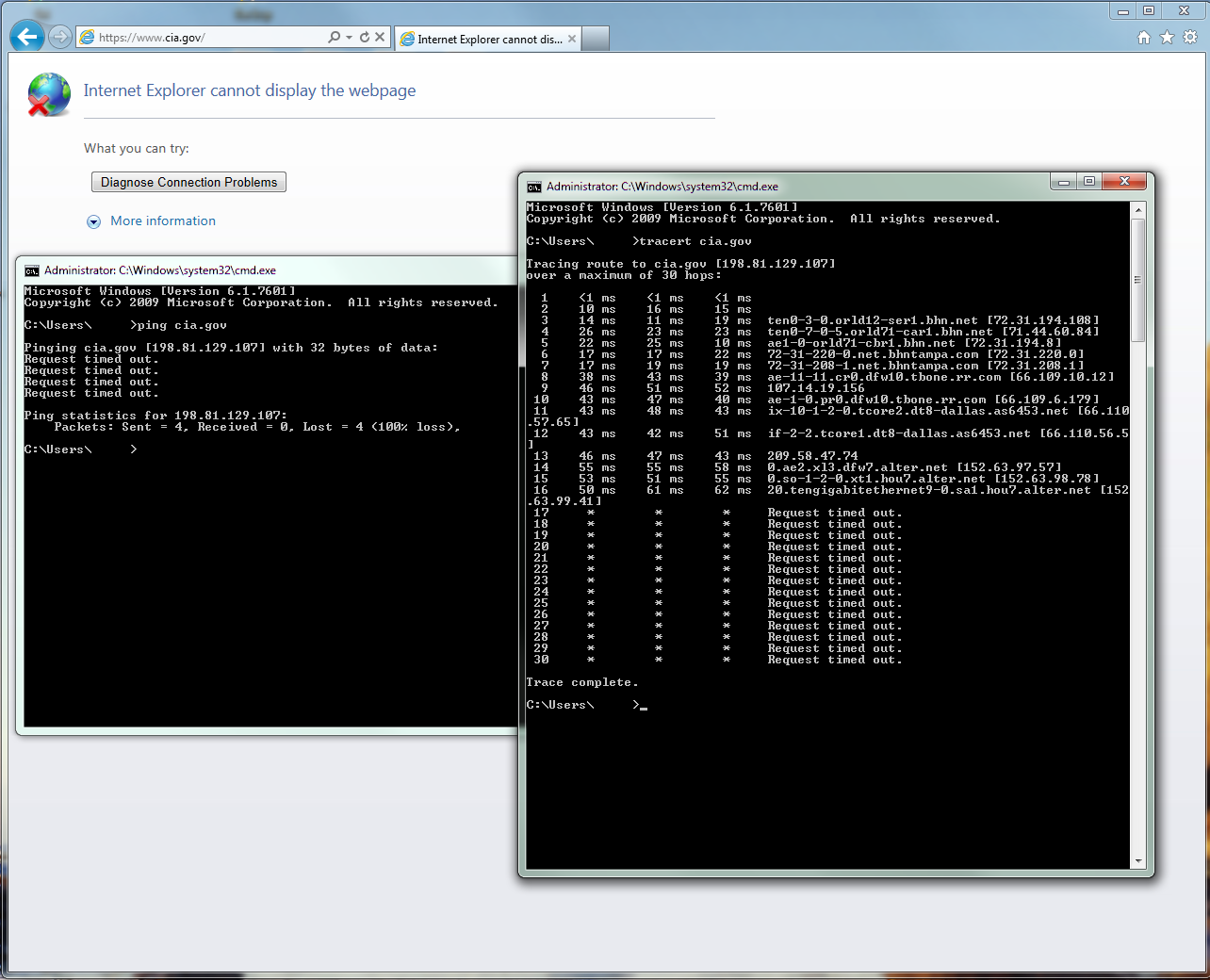
Then again with all the press Anonymous is getting these days I am pretty sure that just about every corporation and government is aware of what they can do when they put their minds to it.
We will keep track of this and will update you if Anonymous ever releases a reason for the takedown.
Discuss this in our Forum
Friday, 10 February 2012 17:25
Anonymous takes down the CIA's Website UPDATE
Written by Sean KalinichReading time is around minutes.
 It looks like Anonymous has succeeded in taking down the website of the CIA. After announcing a tweet at #YourAnonNews stating that the CIA site was about to go down at around 4:14pm the collective appears to have made good on its threat and announced that the site was officially down at 4:45PM.
It looks like Anonymous has succeeded in taking down the website of the CIA. After announcing a tweet at #YourAnonNews stating that the CIA site was about to go down at around 4:14pm the collective appears to have made good on its threat and announced that the site was officially down at 4:45PM.
It looks like this might be a DNS redirect as the IP that CIA.gov resolves to appear to be from the UK and will not resolve on any reverse lookups... More to follow.
Latest from Sean Kalinich
- ConnectWise Slash and Grab Flaw Once Again Shows the Value of Input Validation We talk to Huntress About its Impact
- Social Manipulation as a Service – When the Bots on Twitter get their Check marks
- To Release or not to Release a PoC or OST That is the Question
- There was an Important Lesson Learned in the LockBit Takedown and it was Not About Threat Groups
- NetSPI’s Offensive Security Offering Leverages Subject Matter Experts to Enhance Pen Testing
Leave a comment
Make sure you enter all the required information, indicated by an asterisk (*). HTML code is not allowed.
