According to the Wow Insider on Joystiq, everything if fine and they have many people parroting in with the same line that Blizzard has taken, “it’s all the end users’ fault” what is interesting about these situations is that, from what we have been able to uncover not one of the hacks that supposedly were due to Keyloggers show any sign of banking compromise. Now, if you were able to pull passwords and information through the use a Keyloggers why wouldn’t the criminals go after the bank accounts too? They are not shy about stealing everything in a Diablo III account and turning that into real money, why not hit up any back account information?
For Blizzard to suggest that the issue is all the end-users’ fault is both unprofessional and irresponsible (as are the threats by community managers). It takes a very large number of servers to support the WoW and Diablo III world. Any one of these could be a target for a hack. Even if things are tiered in design (keeping connection, authentication, account information and game world servers separate) there are ways to bridge the gap. When you look at the anatomy of the hacks that have occurred it is almost always due to poor edge security AND improperly configured internal network security.
Many in the press forget that while Blizzard might have great edge security that is not the most logical attack point. Why would someone attempt to punch their way in through their firewalls when there are tens of thousands of connections that legalally pass through that firewall every day. When you work to break into a system you look for openings in the walls that are already there to gain a foothold inside the network. From there you do a little looking around; for internal IP address ranges, host names, operating systems, and other information about the network infrastructure.
With WoW or Diablo this can potentially all be done through the client. The client (although web based) connects a web server that is possibly (although we do not know this for certain) in what they call a DMZ (DeMilitarized Zone). This means that the server is exposed on open internet for connection and as such is much more vulnerable than the internal servers that handle account information and authentication. Now those servers are behind a firewall and safe… well again sort of. When you allow traffic to pass through your firewall from a DMZ you usually create different security zones (in Cisco systems these are security levels and are represented by numbers) and obviously put the DMZ in a “lower” security level than the inside network. So (if Blizzard is using Cisco ASA hardware) you would have the internet set to security level 0, the DMZ set to something like 50 and the internal network set to 100. Your DMZ will also be on a separate IP address range to further isolate it and protect the internal network.
The simple act of doing that allows higher security networks to have access to the lower security networks but not in reverse. To allow information (such as database requests, authentication requests etc.) you have to create rules which allow these connections. These are typically restricted by IP (and in some cases MAC address) and only point to specific servers. In a “best case” design the requests for read information in terms of authentication and database access go to Read-Only copies of the authentication servers and data base. These make it harder for a potential attacker to impact the network and database servers from a compromised server in the DMZ.
Now once authentication takes place read and write access is needed (in case you want to update your account information etc and to apply in-game information/updates). This is the most critical piece of the puzzle and where a typical network would have the most security in place. We have worked on crazy designs that had primary and secondary write servers that were heavily protected before information was written back to the main database servers (after running the information through multiple scans looking for attempted injection attacks etc). We would honestly expect no less from a company like Blizzard, but still their system IS being compromised as is indicated by the sheer number of compromised accounts.
This could mean a couple of things:
One – the connection to the Blizzard servers for authentication is not secure.
Two – Someone has found a way to read authentication information off of the servers during the authentication stage.
Now this may seem like a bold claim, but let’s look at the situation. If a single edge server is compromised someone can read the data packets that are traveling from there through the firewall to any existing authentication servers. At this point you do not have to put keyloggers on thousands of accounts. You only have to skim data off of the edge server as it passes through.
Now this is all theory (and something of an oversimplification of security) as we do not know exactly how Blizzard has built their network (or the hardware used in it) but it does provide a perfect example of how someone can use the system to great effect and to grab user information at a single point. Hacking an edge server is also much easier than trying to monitor thousands of individual user accounts to skim their data. Instead you pull from one or two sources and harvest en masse.
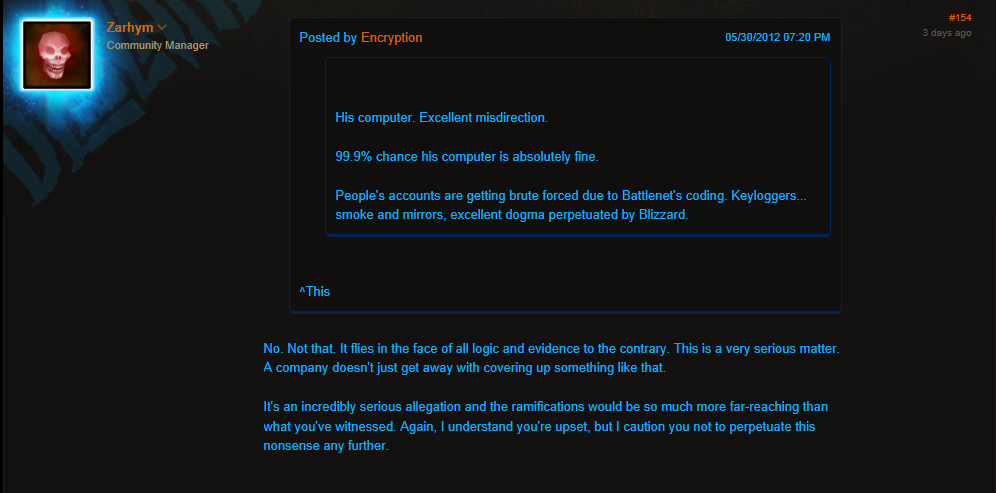
We have noticed that Blizzard is very carefull with what they are saying using statements like: “What I can still confirm is that our database hasn't been brute-force hacked, nor has the personal information of our playerbase been compromised in anyway on our end. We're not kidding when we always say account security is very important to us. If we found any evidence that even a single account's login information was stolen from us, or our databases were otherwise vulnerable to attack, we'd inform our players and do whatever it'd take to lock everything down. “
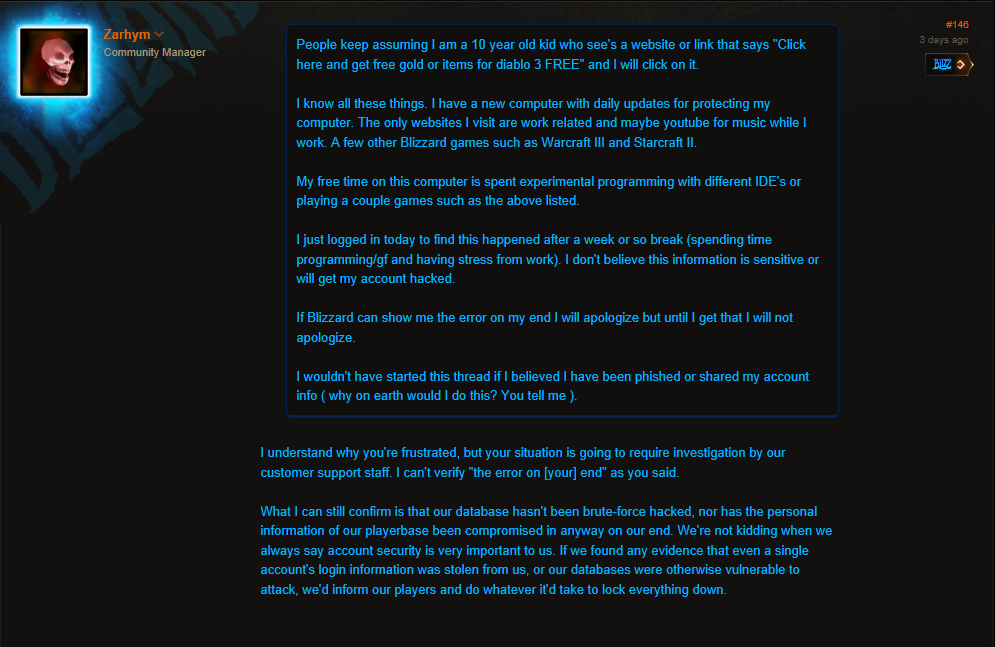
They are right, in the scenario I described above the database in not touched at all except for normal transactions. The comment “nor has the personal information of our playerbase been compromised in anyway on our end” Is interesting because again they are saying that no one has gotten to the authentication servers and hacked them. It does not address the possibility of an edge based attack or that someone is skimming traffic to and from another server (perhaps a server that hosts a specific world or again the edge web servers). All we see here is that Blizzard does not know what is happening and as such they are automatically blaming the people that are using the game. Again this move is both unprofessional and ignorant on their part. What Blizzard needs to do now is to acknowledge the possibility of a compromise of the system and then do an actual investigation to identify what is happening, perhaps even setting up honeypot accounts to see how the compromises are happening in the first place. We just simply cannot believe that every hack has been due to keyloggers and malware, it is exceptionally unlikely. Additionally if this were the case we are fairly confident that end users would also see problems with their bank accounts as well.
Discuss this in our Forum

 Activision Blizzard is striking back at all of the recent press claiming that they (Blizzard) have a serious security issue. As we have told you before their actions of blaming the users and claiming that the thousands of compromised accounts are all due to spyware and keyloggers (without any proof of this by the way) is part of their
Activision Blizzard is striking back at all of the recent press claiming that they (Blizzard) have a serious security issue. As we have told you before their actions of blaming the users and claiming that the thousands of compromised accounts are all due to spyware and keyloggers (without any proof of this by the way) is part of their