From The Blog
-
ConnectWise Slash and Grab Flaw Once Again Shows the Value of Input Validation We talk to Huntress About its Impact
Written by Sean KalinichAlthough the news of the infamous ConnectWise flaw which allowed for the creation of admin accounts is a bit cold, it still is one that…Written on Tuesday, 19 March 2024 12:44 in Security Talk Read 715 times Read more...
-
Social Manipulation as a Service – When the Bots on Twitter get their Check marks
Written by Sean KalinichWhen I started DecryptedTech it was to counter all the crap marketing I saw from component makers. I wanted to prove people with a clean…Written on Monday, 04 March 2024 16:17 in Editorials Read 1590 times Read more...
-
To Release or not to Release a PoC or OST That is the Question
Written by Sean KalinichThere is (and always has been) a debate about the ethics and impact of the release of Proof-of-Concept Exploit for an identified vulnerability and Open-Source…Written on Monday, 26 February 2024 13:05 in Security Talk Read 1125 times Read more...
-
There was an Important Lesson Learned in the LockBit Takedown and it was Not About Threat Groups
Written by Sean KalinichIn what could be called a fantastic move, global law enforcement agencies attacked and took down LockBit’s infrastructure. The day of the event was filled…Written on Thursday, 22 February 2024 12:20 in Security Talk Read 1100 times Read more...
-
NetSPI’s Offensive Security Offering Leverages Subject Matter Experts to Enhance Pen Testing
Written by Sean KalinichBlack Hat 2023 Las Vegas. The term offensive security has always been an interesting one for me. On the surface is brings to mind reaching…Written on Tuesday, 12 September 2023 17:05 in Security Talk Read 2144 times Read more...
-
Black Kite Looks to Offer a Better View of Risk in a Rapidly Changing Threat Landscape
Written by Sean KalinichBlack Hat 2023 – Las Vegas. Risk is an interesting subject and has many different meanings to many different people. For the most part Risk…Written on Tuesday, 12 September 2023 14:56 in Security Talk Read 1870 times Read more...
-
Microsoft Finally Reveals how they Believe a Consumer Signing Key was Stollen
Written by Sean KalinichIn May of 2023 a few sensitive accounts reported to Microsoft that their environments appeared to be compromised. Due to the nature of these accounts,…Written on Thursday, 07 September 2023 14:40 in Security Talk Read 2140 times Read more...
-
Mandiant Releases a Detailed Look at the Campaign Targeting Barracuda Email Security Gateways, I Take a Look at What this all Might Mean
Written by Sean KalinichThe recent attack that leveraged a 0-Day vulnerability to compromise a number of Barracuda Email Security Gateway appliances (physical and virtual, but not cloud) was…Written on Wednesday, 30 August 2023 16:09 in Security Talk Read 2110 times Read more...
-
Threat Groups Return to Targeting Developers in Recent Software Supply Chain Attacks
Written by Sean KalinichThere is a topic of conversation that really needs to be talked about in the open. It is the danger of developer systems (personal and…Written on Wednesday, 30 August 2023 13:29 in Security Talk Read 1903 times Read more...
Recent Comments
- Sean, this is a fantastic review of a beautiful game. I do agree with you… Written by Jacob 2023-05-19 14:17:50 Jedi Survivor – The Quick, Dirty, and Limited Spoilers Review
- Great post. Very interesting read but is the reality we are currently facing. Written by JP 2023-05-03 02:33:53 The Dangers of AI; I Think I Have Seen this Movie Before
- I was wondering if you have tested the microphone audio frequency for the Asus HS-1000W? Written by Maciej 2020-12-18 14:09:33 Asus HS-1000W wireless headset impresses us in the lab
- Thanks for review. I appreciate hearing from a real pro as opposed to the blogger… Written by Keith 2019-06-18 04:22:36 The Red Hydrogen One, Possibly One of the Most “misunderstood” Phones Out
- Have yet to see the real impact but in the consumer segment, ryzen series are… Written by sushant 2018-12-23 10:12:12 AMD’s 11-year journey to relevance gets an epic finish.
Most Read
- Microsoft Fail - Start Button Back in Windows 8.1 But No Start Menu Written on Thursday, 30 May 2013 15:33 in News Be the first to comment! Read 116533 times Read more...
- We take a look at the NETGEAR ProSafe WNDAP360 Dual-Band Wireless Access Point Written on Saturday, 07 April 2012 00:17 in Pro Storage and Networking Be the first to comment! Read 87518 times Read more...
- Synology DS1512+ Five-Bay NAS Performance Review Written on Tuesday, 12 June 2012 20:31 in Pro Storage and Networking Be the first to comment! Read 82058 times Read more...
- Gigabyte G1.Sniper M3 Design And Feature Review Written on Sunday, 19 August 2012 22:35 in Enthusiast Motherboards Be the first to comment! Read 80344 times Read more...
- The Asus P8Z77-M Pro Brings Exceptional Performance and Value to the Lab Written on Monday, 23 April 2012 13:02 in Consumer Motherboards Be the first to comment! Read 71008 times Read more...
 It is a parent’s nightmare and something that happens more often that many colleges and bars would care to admit; drugging some girls drink in order to take advantage of her. We as parents go through the litany; never accept a drink from anyone, never let your drink out of your site,… if you are a parent or have a little sister you know the drill.
It is a parent’s nightmare and something that happens more often that many colleges and bars would care to admit; drugging some girls drink in order to take advantage of her. We as parents go through the litany; never accept a drink from anyone, never let your drink out of your site,… if you are a parent or have a little sister you know the drill.
Well, now in addition to good advice, common sense (a stun gun, martial arts training, a body guard…) you can also give your daughter, sister (or even wife) something else to help. Some geniuses in Israel have come up with a device that can detect the most common drugs used in date rape crimes. The device is disguised to look like a swizzle stick or a straw so that the perpetrator is not aware that you are looking for anything. Inside the device is a solution that changes color in the presence of GHB (gamma-hydroxybutyric acid) and Ketamine for now, but the manufacturers are working to add even more.
They have even added a light to it so that you can use it in dark places. So far the accuracy rate has been 100% which seriously impressive. It is a brilliant idea and one that I hope they can add a few things into; like the ability to shoot a toxic dart at the person that put the drug in, or burn them with acid… hey I can dream can’t I?
Source CNET
Discuss in our Forums
 It seems that some members of the AntiSec group have recently released a large amount of information about law enforcement officers to include their names addresses, social security numbers and in some cases credit card information. Now, I have no love at all for corrupt police officers or ones that abuse their position of authority, but exposing their personal information puts innocents at risk.
It seems that some members of the AntiSec group have recently released a large amount of information about law enforcement officers to include their names addresses, social security numbers and in some cases credit card information. Now, I have no love at all for corrupt police officers or ones that abuse their position of authority, but exposing their personal information puts innocents at risk.
You see the bad guys rarely go after the officer in question directly. No, they go after the family the wife, kids etc. So while I have never had an issue with the things that Anonymous have done in the past. For the most part they go after corporate entities that have no respect for the consumer or anyone else for that matter. However this particular portion of the group has stepped over a line that will lose them appeal from the average person. Now the media can claim they have put innocent people at risk (and they have in truth).
Anonymous was better off when they were going after the corporations and the government instead of releasing information of this type. Of course on the other side of the coin, I also put blame on the people hosting these sites as they are responsible for protecting that information and failed in that duty not once but twice.
Discuss this in our Forum
GIGABYTE Announces Entire 6 Series Ready to Support Native PCIe Gen. 3
Written by Sean Kalinich
- GIGABYTE Announces Entire 6 Series Ready to Support Native PCIe Gen. 3 -
-- Future Proof Your Platform for Next Generation Intel 22nm CPUs --
 |
City of Industry, California, August 8, 2011 - GIGABYTE TECHNOLOGY Co., Ltd, a leading manufacturer of motherboards, graphics cards and computing hardware solutions today announced their entire range of 6 series motherboards are ready to support the next generation Intel 22nm CPUs (LGA1155 Socket) as well as offer native support for PCI Express Gen. 3 technology, delivering maximum data bandwidth for future discrete graphics cards.
Wanting to provide maximum upgradeability to customers, GIGABYTE has enabled native support for PCI Express Gen. 3 across the entire range of GIGABYTE 6 series motherboards, including the recently launched G1.Sniper 2 motherboard, when paired with Intel’s next generation 22nm CPUs. By installing the latest BIOS for their 6 series motherboards today, users can be assured they are ready to take advantage of all the performance enhancements tomorrow’s technologies have to offer.
To future proof your GIGABYTE 6 series motherboard, please download and install the latest BIOS update for your motherboard model from the GIGABYTE website: www.gigabyte.us.
GIGABYTE 22nm CPU and PCIe 3.0 Ready Motherboards
|
Chipset |
Model |
BIOS |
|
Z68 |
G1.Sniper 2 |
F3 |
|
Z68X-UD7-B3 |
F8 |
|
|
Z68XP-UD5 |
F3 |
|
|
Z68X-UD5-B3 |
F8 |
|
|
Z68XP-UD4 |
F3 |
|
|
Z68X-UD4-B3 |
F8 |
|
|
Z68XP-UD3P |
F4 |
|
|
Z68X-UD3P-B3 |
F6 |
|
|
Z68XP-UD3R |
F3 |
|
|
Z68X-UD3R-B3 |
F4 |
|
|
Z68X-UD3H-B3 |
F7 |
|
|
|
Z68XP-UD3 |
F4 |
|
Z68MX-UD2H-B3 |
F8 |
|
|
Z68A-D3H-B3 |
F9 |
|
|
Z68MA-D2H-B3 |
F7 |
|
|
P67/H67 |
P67A-UD7-B3 |
F5 |
|
P67A-UD5-B3 |
F6 |
|
|
P67A-UD4-B3 |
F5 |
|
|
P67A-UD3P-B3 |
F5 |
|
|
P67X-UD3R-B3 |
F4 |
|
|
P67A-UD3R-B3 |
F5 |
|
|
P67X-UD3-B3 |
F5 |
|
|
P67A-UD3-B3 |
F5 |
|
|
P67A-D3-B3 |
F4 |
|
|
P67-DS3-B3 |
F2 |
|
|
PH67A-UD3-B3 |
F5 |
|
|
PH67-UD3-B3 |
F4 |
|
|
PH67-DS3-B3 |
F2 |
|
|
PH67A-D3-B3 |
F4 |
|
|
H67A-D3H-B3 |
F5b |
|
|
H67M-D2-B3 |
F5a |
|
|
H67N-USB3-B3 |
F6e |
|
|
H61 |
H61M-D2P-B3 |
F6f |
|
H61M-D2-B3 |
F7e |
|
|
H61M-S2V-B3 |
F5g |
|
|
H61M-USB3-B3 |
F8h |
|
|
H61M-S2-B3 |
F2h |
|
|
H61N-USB3-B3 |
F2c |
|
|
HA65M-D2H-B3 |
F8o |
|
|
P61-S3-B3 |
F4c |
|
|
P61-DS3-B3 |
F3b |
|
|
P6-USB3-B3 |
F8d |
|
|
PA65-UD3-B3 |
F8c |
Share the news to Facebook and Twitter
![]()
![]()
About GIGABYTE
GIGABYTE Technology Co. Ltd., headquartered in Taipei, Taiwan, is known as a leading brand in the IT industry with branch offices located in 24 countries around the world. Founded in 1986, GIGABYTE started as a small research and development team and has since taken a position as one of the in the world's top motherboard manufacturers. In addition to motherboards and graphics cards, GIGABYTE further expanded its product portfolio to include notebook and desktop PCs, datacenter servers, networking products, mobile handsets, and home entertainment devices to serve each facet of the digital life in the home and office. Everyday GIGABYTE aims to “Upgrade Your Life” with innovative technology, exceptional quality, and unmatched customer service. Visit www.gigabyte.us for more information.
Why Pottermore is one of the most brilliant marketing schemes ever
Written by Sean Kalinich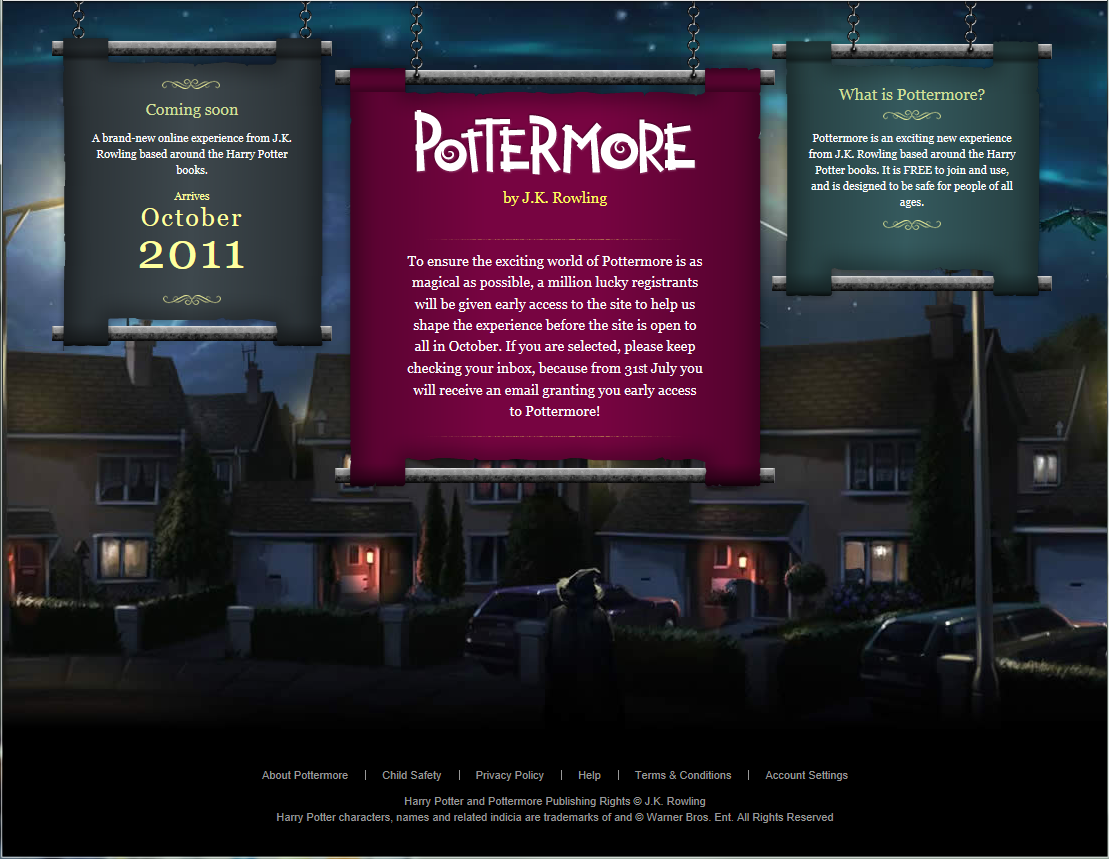 If you have not heard of Harry Potter then you have been living under a rock. The Boy Wizard has become this generations Star Wars. The series of seven books has amassed a serious number of followers (I have read them) while the movies have spawned a monster of a merchandising machine.
If you have not heard of Harry Potter then you have been living under a rock. The Boy Wizard has become this generations Star Wars. The series of seven books has amassed a serious number of followers (I have read them) while the movies have spawned a monster of a merchandising machine.
As I live in Florida I have visited the Wizarding World of Harry Potter at Universal Studio’s Islands of Adventure more than once and after being open for almost a year there is still a multi-hour wait to get into some of the stores. However, even though the creator of this phenomenon makes a good deal of money from all of this it is not as much as she could.
The solution? Well J.K. Rowling has teamed up with Sony Entertainment to create an online virtual world called Pottermore. In this new virtual world they are extending the world created in the books to allow fans (both young and old) to take on new personalities and experience the world of Hogwarts (the best Wizarding School in Brittan and pretty much the central location in the books. Officially the new site opens up in October, but ever since it was announced they have teased about a close Beta beginning on July 31st. At first all you had to do was submit an e-mail before July 31st.
However, because of that most people submitted the e-mail and that was that. People still visited Pottermore.com but it was not as much as it could have been (at least from what we are hearing). So how do you fix that? Again a simple answer. You change your mind before the morning of the 31st.
Fans began to hear that for the Beta there was only going to be 1 million people allowed to enter. Now that is a pretty big number until you realize that more than a million people went to see Harry Potter and the Deathly Hallows Part 2 (the final film in the series) on opening weekend and it is still going strong many weeks later.
So, on the morning of the 31st at 8am London time fans flocked to Pottermore.com in the hopes to be one of the few to get in. However, the powers that be changed their minds once again. Instead of letting people in they were going to have a multiday (seven for the seven books to be exact) scavenger hunt (maybe they stole that idea from us…). On each day you would have to hit the site by 8am London time (3am Eastern Time in the US) and try to find something called the Magic Quill. Each day a clue (a question that could be answered if you have access to or have read the books) would be posted on Pottermore.com. This Clue would give you a site to go to at Pottermore.com. There you could click on a flash image that of the Magical Quill and you could put your name in for the Beta. Even if you had the answer you had to be quick. If you did not get your submission in before that days allotted number of positions was filled you were out of luck.
But wait! There were still four more days so everyone that did not get in check back tomorrow! As you can see what Sony has done is create a site that is going to have other companies clambering to put ads on it. Before the site is even live they have found a way to get multiple millions of hits (perhaps even tens of millions). From what we are hearing although the early entries are done no one has actually gotten into the site. In order to do so you have to wait for an e-mail to arrive with a special link to gain access to the site. While everyone waits they are still going back multiple times every day to see if anything has changed. Can you imagine the advertising allure of a site like this, especially one that is already geared towards kids and teens? J.K. Rowling may truly want to create something for the fans of her books, but I am certain that the executives at Sony are seeing nothing but dollar signs at this point.
Discuss this in our Forum
*updated 08-08-2011 17:46PM EST with correction on number of days the magic quill was available
 At Defcon 19 in Las Vegas this year the annual security show launched a new event. Called Defcon Kids the even features young “hackers” that have uncovered exploits, vulnerabilities and other security related items. One of the first to speak this year is a 10-Year Old Girl from California who found an exploit in some mobile games.
At Defcon 19 in Las Vegas this year the annual security show launched a new event. Called Defcon Kids the even features young “hackers” that have uncovered exploits, vulnerabilities and other security related items. One of the first to speak this year is a 10-Year Old Girl from California who found an exploit in some mobile games.
The girl, who goes by the alias CyFi (and who is a Girl Scout as well) found the new exploit because she did not want to wait for certain in-game items to complete in a farming game that she plays. To get around this boring wait she simply moved time along. When she did this it opened up the exploit. Independent researchers have verified her findings, but will not list the games that are affected by this (no will CyFi giving the authors a chance to fix things).
CyFi also said that while many games have cheat prevention systems she found that most can be circumvented with a few simple techniques. The Exploit affects both iOS and Android operating systems and illustrates how developers and security experts alike can miss something simple while overthinking their protections and applications.
Source and Image Cnet
Discuss thus on our Forum
Gigabyte's 990FXA-UD5 performs for us in the Lab Featured
Written by Sean Kalinich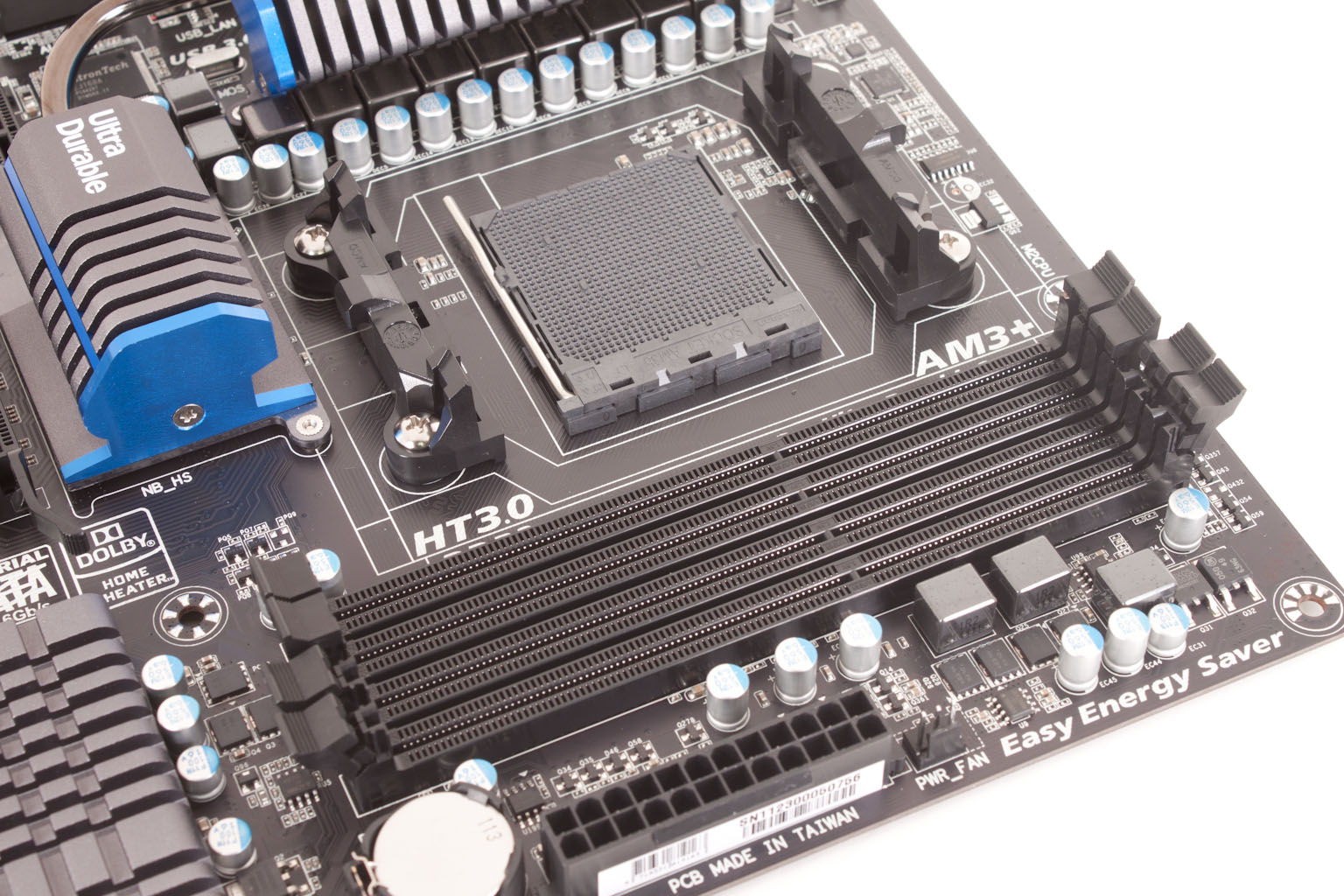 We have taken our walk around of the Gigabyte 990FXA-UD5 and found we like the design and many of the features packed into the system. In the second half of our test we will be diving into what you can get out of it when you put in under the stress of rendering, gaming and general purpose computing. We do have concerns with this new product as it has really been built with a newer CPU in mind (one that is not ready as of this writing). Still one of the things that AMD has always worked on is backwards compatibility. With that in mind we are breaking out our Phenom II 1100T and getting ready for some testing.
We have taken our walk around of the Gigabyte 990FXA-UD5 and found we like the design and many of the features packed into the system. In the second half of our test we will be diving into what you can get out of it when you put in under the stress of rendering, gaming and general purpose computing. We do have concerns with this new product as it has really been built with a newer CPU in mind (one that is not ready as of this writing). Still one of the things that AMD has always worked on is backwards compatibility. With that in mind we are breaking out our Phenom II 1100T and getting ready for some testing.
 As the Black Hat security conference is going on this week we will be covering a lot of the exploits they find. We have already talked about the SCDA vulnerability, how cars with remote lock/unlock/start are vulnerable and even touched in HTML5 and mobile phone exploits. Now we hear confirmation of something we have known for a while: Apple’s OSX server is not secure.
As the Black Hat security conference is going on this week we will be covering a lot of the exploits they find. We have already talked about the SCDA vulnerability, how cars with remote lock/unlock/start are vulnerable and even touched in HTML5 and mobile phone exploits. Now we hear confirmation of something we have known for a while: Apple’s OSX server is not secure.
Experts at the security firm Isec have shown that while individual systems can be secured (the called them islands) once you put the OSX server in play it is “two notches above trivial” to compromise the whole network. Isec showed this off by executing a local DNS exploit that allowed them to scavenge admin credentials and then gain full admin access to the network.
All was not bad news for Apple fans; Isec also said that OSX Lion now “matches” Microsoft’s Windows 7 for local permissions elevation protection and anti-exploit protection. Isec also went on to say that Apple’s marketing has been training consumers to feel safe when using Macs which actually makes them more likely to be open to targeted attacks.
Gigabyte and HWBot kicks off the A75 OC Challenge
Written by Sean Kalinich Now that the AMD Llano CPU with its Fusion architecture is out and we have seen some of what it can do you knew it would only be a matter of time before the call to overclock this new CPU was put out.
Now that the AMD Llano CPU with its Fusion architecture is out and we have seen some of what it can do you knew it would only be a matter of time before the call to overclock this new CPU was put out.
Gigabyte is partnering up with HWBot for their A75 OC Challenge. This new overclocking contest is simple; Gigabyte wants you to push this new CPU+APU to it limits using any Gigabyte A75 Based motherboard.
There will be 5 stages you will have to submit clocks and scores for,
Stage 1 – 3DMark11 Performance Preset
Stage 2 – 3DMark Vantage Performance Preset
Stage 3 – PCMark 7
Stage 4 - Unigine Heaven DX11
Stage 5 – UCBench 2011
This contest will continue through the month of August. For more information check out the full PR
Discuss and talk tactics on our Forum
-- GIGABYTE Announces “A75 OC Challenge” on HWBOT--
Written by Sean Kalinich
-- GIGABYTE Announces “A75 OC Challenge” on HWBOT--
-- How Quick are You with an APU? –
City of Industry, California, August 4th 2011 – GIGABYTE TECHNOLOGY Co., Ltd, a leading manufacturer of motherboards, graphics cards and other computing hardware solutions today announced a new overclocking competition in conjunction with HWBOT.org called the “A75 OC Challenge” during the month of August.
Since the recent launch of the world’s first APU (Accelerated Processing Unit) from AMD, there has been a lot of benching going on to see if AMD really has created an onboard graphics solution that can compete head-to-head with the lower end discrete market. But many are asking the age-old question, “will it blend”? No, wait a second...we really don’t suggest trying that. The real question is will it overclock? During the month of August, GIGABYTE would like you guys to answer that for us. So, using any GIGABYTE A75 motherboard (learn all about them HERE), submit your best scores for each of the 5 stages using only the APU graphics…ie., no discrete graphics cards allowed. Since HWBOT is hosting, HWBOT rules apply. The first place winner gets a 990FXA-UD5 and second and third place each get a E350N-USB3. Good luck everyone!
Stage 1: 3Dmark 11 P (Preset)
Stage 2: 3Dmark Vantage P (Preset)
Stage 3: PCMARK 7
Stage 4: Unique Heaven DX11
Stage 5: UCBench2011
For complete contest details and rules, please visit: http://hwbot.org/competition/gigabyte_apu_contest
About GIGABYTE Upgrade Your Life
GIGABYTE, headquartered in Taipei, Taiwan, is known as a global leading brand in the IT industry, with employees and business channels in almost every country. Founded in 1986, GIGABYTE started as a research and development team and has since taken the lead in the world's motherboard market. On top of motherboards and graphics accelerators, GIGABYTE further expanded its product portfolio to include notebook and desktop PCs, digital home entertainment appliances, networking servers, communications, mobile and handheld devices, servicing every facet of people's lives at home or business. Everyday GIGABYTE aims to “Upgrade Your Life” with the most innovative designs and impeccable quality and services. Visit http://www.gigabyte.us for more information.
Follow GIGABYTE on:
![]()
![]()
Genius Introduces the Upgraded G-Pen F610 Ultra Slim Graphic Tablet
Written by Sean KalinichGenius Introduces the Upgraded G-Pen F610 Ultra Slim Graphic Tablet
Now Available in the USA & Canada
Convenience, Control plus Sleek Design
August 4, 2011, Taipei, Taiwan – After its successful debut of the first G-Pen F610 Writing Graphic Tablet, the leading manufacturer of computer peripherals Genius launches an upgraded version with the latest software & package for Windows 7, expected to create yet another heat wave in the market.
As an ultra-slim, 6” x 10” wireless text graphic-design tablet, the Genius G-Pen F610 offers better control than a conventional mouse and a stylish, slim design. The tablet pairs perfectly with either a Mac or PC computer, offering a functional as well as aesthetic tool for taking notes, handling emails (including handwritten emails), handwriting recognition, and professional graphics design.
Genius' G-Pen F610 Tablet makes work more efficient with its 29 programmable “Hot-Key” areas to set up shortcuts for word processing, Internet and operating system tasks. Simply plug the unit into your computer and enjoy built-in, Vista-like functions, such as pen flick navigation. The G-Pen F610 Writing Graphic Tablet works with any screen size, and is perfect for flat and wide screens.
The smart-looking pen packaging along with the Genius G-Pen F610 boasts two buttons and 1024-level pressure sensitivity, allowing graphic artists the subtlety of more pressure levels. The two pen buttons can be programmed to function as left- and right-click mouse buttons. Since the pen battery can last up to one year, the odds of a “power outage” during important work projects are highly unlikely. The pen also comes with a holder that protects the device and its tip, and keeps it handy for use.
The Genius G-Pen F610 includes the following:
- G-Pen F610 tablet
- Cordless pen
- Quick installation guide
- Two additional pen tips & tweezers
- Macro Key Manager
- Power Presenter RE/Free Notes & Office Ink
- PhotoImpact 12SE
- Mac Driver
- One AAA battery included allowing the Tablet to be used right out of the box.
System Requirements:
- IBM PC/Pentium 233 compatible or higher
- Windows Vista/XP/2000
- Macintosh with OS x 10.2.8 or later
- Available USB port
- CD/DVD-ROM drive for software installation
The suggested retail price for the Genius G-Pen F6 Graphic-design Tablet is US$99.90.
More product details are available at:
http://geniusnet.com/wSite/ct?xItem=16834&ctNode=174
About Genius
Genius is an international leading brand in computer peripherals. Established by KYE Systems Corp. in 1983, Genius offers PC products including computer mice, keyboards, web and security cameras, speakers, gaming peripherals, remote controls, headphones, digital cameras, digital camcorders and digital photo frames. Genius also expanded from computer peripherals into consumer electronic products that include mobile phone accessories, Bluetooth headsets and iPod speakers. Since 2007, Genius has been one of Taiwan’s top 20 Global Brands. For more information you can visit the Genius website at www.geniusnet.com.
Where to buy Genius products:
http://www.geniusnet.com/wSite/sp?xdUrl=/wSite/whereToBuy/whereToBuy.jsp®ion=AM&xAbstract=AM28&mp=4
More...
 Remember how we told you about that some of the world’s most sensitive infrastructure hardware could be vulnerable by simply searching for them on Google? Well now we hear that even your car can be compromised with the right gear, as a group of security experts showed at Black Hat in Las Vegas. By setting up their own GSM network (granted not an easy task) the group was able to unlock and then start a Subaru SUV.
Remember how we told you about that some of the world’s most sensitive infrastructure hardware could be vulnerable by simply searching for them on Google? Well now we hear that even your car can be compromised with the right gear, as a group of security experts showed at Black Hat in Las Vegas. By setting up their own GSM network (granted not an easy task) the group was able to unlock and then start a Subaru SUV.
What they did was to capture authentication messages sent from the control server to the car. Once they had these in hand they were able to send commands to the car using an Android based smart phone and that was pretty much it.
As more and more of the world goes wireless you have to worry about what security is (and can honestly be put) in place to protect from this type of attack. It is not uncommon for banks to run wireless as a backup (that is still open and in a passive state) many security cameras will operate over 3G now as well. With the SCDA vulnerability and one I have recently heard of that affects banking applications on both Android and the iPhone you have to wonder just who is in charge of keeping these things safe?
Source Engadget
Discuss this on our Forum
Facebook Facial Recognition API Declared Illegal in Germany
Written by Sean Kalinich There are times when companies just forget about the impact to consumers. Most times these little oversights are caught and removed before the products or services are dropped on the unsuspecting consumers. Still there are times when these things get pushed out because the company in question is too big or too arrogant to believe they can’t do what they want.
There are times when companies just forget about the impact to consumers. Most times these little oversights are caught and removed before the products or services are dropped on the unsuspecting consumers. Still there are times when these things get pushed out because the company in question is too big or too arrogant to believe they can’t do what they want.
A good example of this is Google Street View. There is nothing like a free service that allows anyone to see your home, the cars you drive etc. Google even had the temerity to send their cars onto clearly marked private roads.
Now let’s move forward to today, Facebook wants to put facial recognition software into their API to quickly tag people in photographs. The problem is that this software collects data about the people in the pictures. There is also no easy way to remove this data by the user. Facebook thinks that collecting this and other data is ok (as it is not in violation of any US law which are notorious for not protecting privacy or fair usage). However, Facebook did not count on some very strict (as they should be) privacy laws in Germany. Germany has actually declared the new feature illegal and is going after Facebook to disable the feature and to remove all data collected by the service.
I only wish that there were laws this protective of the average citizen in the US.
Source Fudzilla
Discuss this on our Forum
 In what has to be humorous to those of us that called this last year (yes I was one of them) it has now come out that HTML5 is more full of holes than your average sieve. According to a study out now it appears that HTML5 opens up some serious risks including allowing malicious code to execute cross-domain APIs, ClickJacking, Frame impersonation and worse. One of the problems is that HTML5 (like many other things from Apple) is not compatible with other standards on the net. Some of the “security” features that exist on to prevent cross scripting and window framing (where you put a frame inside a legitimate window to execute malicious code) are rendered useless by the technology in HTML5.
In what has to be humorous to those of us that called this last year (yes I was one of them) it has now come out that HTML5 is more full of holes than your average sieve. According to a study out now it appears that HTML5 opens up some serious risks including allowing malicious code to execute cross-domain APIs, ClickJacking, Frame impersonation and worse. One of the problems is that HTML5 (like many other things from Apple) is not compatible with other standards on the net. Some of the “security” features that exist on to prevent cross scripting and window framing (where you put a frame inside a legitimate window to execute malicious code) are rendered useless by the technology in HTML5.
Other items that are bundled into the code are vulnerabilities that allow a service to register itself as a content handler without notifying the user, and a caching API that can be skimmed to collect user information (location, time of last visit and possible the actual page visited) in much the same way that Google’s Chrome browser can. In all there are some 50 Vulnerabilities that were listed in the report which is of serious concern considering Apple’s push to put this technology in place. Perhaps Apple feels that they can ignore these and continue on with their charmed life, or that their OS would be impervious to any threats. No matter the cause, considering Steve Jobs’ impassioned rants about Adobe and how their products are security risks it is more than a little amusing.
Source The Inquirer
Talk about this in our Forum
Clearwire announces switch to LTE on existing networks
Written by Sean Kalinich Not all that long ago (about a year to be exact) I engaged in a little online debate with someone about LTE Vs WiMax. At the time I was told that LTE was better and that WiMax would be a losing battle. I agreed with the comment about speed, but hastily added that MiMax is not a losing battle. You see the problem is that people often misunderstand that WiMax and LTE are not different hardware technologies (at least not on the backbone) but differ in the protocols used to push the data across that hardware. Clearwire was aware of this when they built their network; they knew that they could get WiMax out now and still shift over faster and for less money than the much of the competition can get LTE off the ground.
Not all that long ago (about a year to be exact) I engaged in a little online debate with someone about LTE Vs WiMax. At the time I was told that LTE was better and that WiMax would be a losing battle. I agreed with the comment about speed, but hastily added that MiMax is not a losing battle. You see the problem is that people often misunderstand that WiMax and LTE are not different hardware technologies (at least not on the backbone) but differ in the protocols used to push the data across that hardware. Clearwire was aware of this when they built their network; they knew that they could get WiMax out now and still shift over faster and for less money than the much of the competition can get LTE off the ground.
The down side is that Clearwire waited too long to start the conversion and have lost quite a bit of money on this deal. Of course they also could have had contractual restrictions that required them to reach a certain level of loss before they could make the shift in existing markets (read Sprint/Nextel)… that is pure guess work on my part but I have heard of worse in business. No matter what the reason the thing is that Clearwire is going to make the switch and will start in their existing markets to make the shift less costly and also to start off building revenue on the investment.
Now we have to figure out if the existing Radios inside the current handsets can be “flashed” to support the LTE protocol.
Source CNET
Discuss in our forum
